CBDCs require governments to put a special focus on security
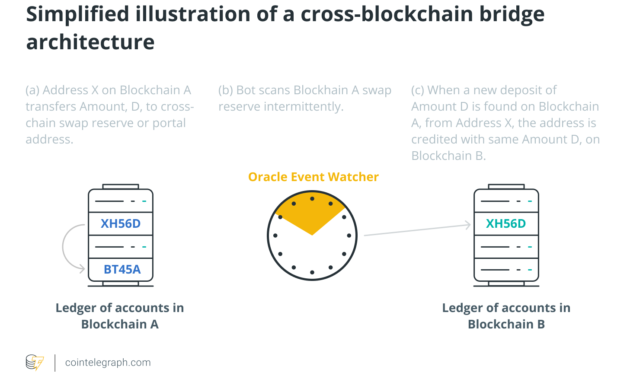
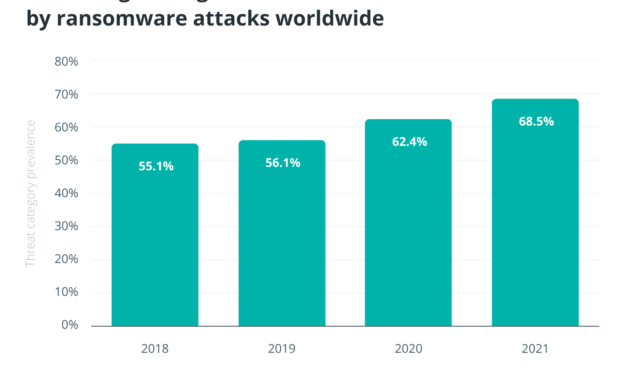
Today’s financial world is becoming increasingly digitized, and naturally, central banks want to adapt to the changing environment. The use of cash is rapidly declining. Globally, the rise of digital payment apps and COVID-19 have only accelerated the decline in cash usage, fueling interest in digital currencies and demand for easier payment solutions.As crypto adoption continues to expand, the idea of central bank digital currencies (CBDCs) has also gained momentum. Governments across the world have been flirting with, and examining, the idea of issuing their own CBDCs, with a handful already launching. It isn’t clear when CBDCs will become normalized. Don’t expect CBDCs to resemble Bitcoin’s (BTC) decentralized characteristics because, by definition, a central bank is a centralized entity. That being said, they can provide some of the same benefits, such as reducing payment verification times and providing proof of transaction. There are, however, still quite a few challenges to overcome.Related: Built to fall? As the CBDC sun rises, stablecoins may catch a shadowAmong these challenges are the operational risks of the “cyber sphere.” While banks are accustomed to investing resources in safeguarding their “fiat” reserves, safeguarding digital currencies requires a different mindset. Blockchain technology has some inherent vulnerabilities — including anonymity and irreversibility — that can be exploited by clever scammers. Although, it’s not clear if CBDCs will leverage blockchain technology. Could CBDCs potentially expose central banks to new types of cyber threats? And how would these potential threats or vulnerabilities manifest themselves?Cybersecurity isn’t easyHackers have become increasingly sophisticated and brazen in their attacks over the last few years. Both traditional finance and blockchain protocols find themselves victims of malicious intent. In fact, Denmark’s central bank was hacked as part of the SolarWinds operation in late 2020. This should sound alarm bells for governments everywhere. Imagine a group of dedicated hackers finds, penetrates and gains access to a backdoor that gives them control of the central bank’s private key. Private keys are the most important elements of a blockchain system, as any transactions conducted with the private key are registered by the system as valid and secure. At this point, the bulk — or a significant chunk — of the country’s treasury could effectively be held hostage by a criminal organization. The hacker could mint or burn digital currency at will.An influx or reduction in a digital currency could affect the value of the genuine currency, have an impact on consumers through inflation, and lead to monetary losses for companies. A breach to this extent could be catastrophic and potentially lead to the devastation of the nation’s entire economy. Of course, an attack of this scale would be far too advanced for even some of the most talented criminal masterminds, but the threat cannot be dismissed. Such an attack would be unprecedented, so predicting the aftermath is anyone’s guess. But it wouldn’t be pretty: The world’s economic and political order and stability would, undoubtedly, be tested.Clearly, any government would spend top dollar on cyber defenses to protect its newly established digital infrastructure. But simply investing an abundance of resources isn’t a guarantee against hacks. Naturally, any central bank launching a digital currency would be an attractive target.So how can a country that is determined to launch its own CBDC protect its treasury from criminals trying to steal it? Securing the national treasuryDisincentivizing malicious cyber attackers is no easy task — they are always on the lookout for new and rewarding targets while exploiting the slightest vulnerabilities. Crypto hackers are adept at identifying attack surfaces, exploiting them, injecting malicious code, and taking control of individuals’ and organizations’ private keys. Banks invest millions, if not billions, each year to defend their databases and IT infrastructure. Various security layers are employed to protect against hackers, inside jobs or unintentional leakage of sensitive information. While banks are familiar with information security, safeguarding digital assets requires a vastly different approach than traditional assets. If they decide to leverage blockchain, central banks must consider how existing banking frameworks can be adapted to blockchain’s distributed architecture, with extra attention paid to the system architecture, governance and consensus mechanisms. When it comes to safeguarding a nation’s treasury, there is no such thing as “too secure.” In the case of CBDCs, banks must take great measures to protect and defend their private keys. Today’s custody solutions have come a long way, and yet, almost all of them suffer from the same deficit. Due to the anatomy of a blockchain transaction, all transactions must be conducted while connected to the internet at some point.Related: US central bank digital currency commenters divided on benefits, unified in confusionThis connectivity is their single point of failure and the reason they cannot be 100% secure. It is suggested that governments find a “never internet-connected” solution to store and manage the private keys while issuing the CBDCs, providing custody and conducting on-chain settlements. Most central banks are rightfully taking their time and conducting all the necessary due diligence to weigh the risks and rewards of CBDCs properly. Some may actually decide to push off their involvement, especially given the crypto market’s volatility. But any nation implementing a CBDC in the near future must make sure it’s ready to defend its digital assets and, most importantly, its private keys. When it comes to blockchain, central banks should completely rethink everything they know about IT security needs. Only then can they launch their digital currencies with enough peace of mind.Lior Lamesh is the co-founder and CEO of GK8, a blockchain cybersecurity company that offers a custodial solution for financial institutions. Having honed his skills in Israel’s elite cyber team reporting directly to the prime minister’s office, Lior led the company from its inception to a successful acquisition for $115 million in November 2021. In 2022, Forbes put Lior and his business partner Shahar Shamai on its 30 Under 30 List.
Čítaj viac