How Web3 resolves fundamental problems in Web2
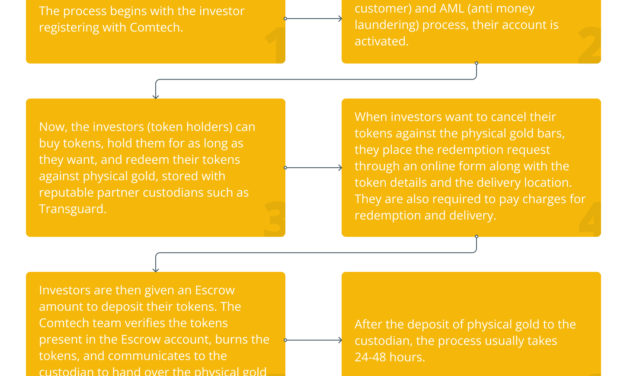
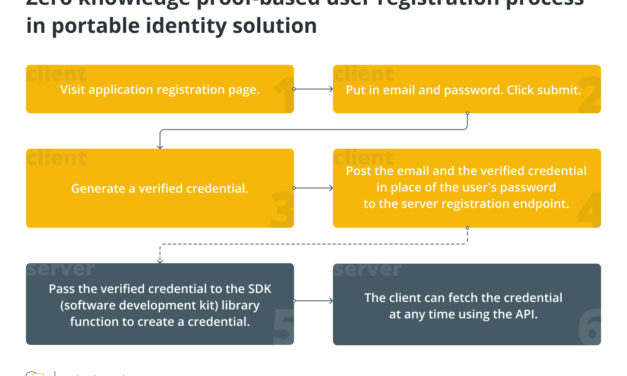
Web3 returns content rights to the author, enhances the security level, eliminates unfair censorship, ushers in transparency, automates the functioning of software and facilitates a creator economy. Thanks to the characteristics of Web3, businesses can take advantage of opportunities that are beyond imagination. Concepts like decentralization and permissionless cybersphere were just in sci-fi. Nonetheless, Web3 hopes to resolve the problems in Web2, paving the way to a decentralized era in the internet. Data ownership Decentralization puts greater control in the hands of users, ending the monopoly of Big Tech. Users can decide whether they want to share their data or keep it private. The fact that computing power and decision making is diversified makes the system inherently more stable than centralized systems where the whole operation is hinged on a cluster of servers or a core decision-making entity or individual. Though several Web2 applications have moved toward multi-cloud hosting, the resilience of projects that are decentralized in real terms is simply at another level. Enterprises can select a topography for their application, depending on their own data landscape and challenges to address. Data security Data stored in a huge centralized database is quite vulnerable. Hackers need to break through just one system to compromise valuable user data. Often, insiders play a role in tipping key information to external malicious players. Decentralized systems are designed to be resistant to such behavior by a section of participants, making security in Web3 more efficient than Web2 systems in keeping data secure. On the contrary, when almost every company is going digital and data-driven, the risk of malicious attacks has risen exponentially as well. In such a scenario, vandalism in cyberspace has become a big threat, threatening monetary and reputation loss. Decentralization enhances the security level, if not eliminating the problems completely. Unfair censorship Centralized systems often subject users to unfair censorship. Decentralization transfers the authority to the participants, making it difficult for any single entity to influence a narrative that doesn’t suit them. A Web2 social media site like Twitter, for instance, can censor any tweet at any time they want. On a decentralized Twitter, tweets will be uncensorable. Similarly, payment services in Web2 might restrict payments for specific types of work. In Web3, censorship will be hard, both for participants with good intent and malicious players. Decentralized web promises control and privacy to all participants. Moreover, network participants can take an active part in the governance of the project by casting votes. Financial freedom In Web3, every participant is a stakeholder. Backed by an array of technologies that inherently resist control, Web3 promotes financial freedom. Decentralized finance (DeFi), where anyone can freely engage in financial activities, is a prime example of the independence participants enjoy. Complying with Know Your Customer (KYC) and Anti-Money Laundering (AML) regulations opens DeFi to new user groups and mass adoption. Moreover, payments in Web2 are made in fiat, while Web3 payments are made through cryptocurrencies, though fiat payment systems can be integrated as well. Transparency Transparency is something built into the design of decentralized ecosystems. Nodes work in tandem to ensure the frictionless functioning of the system and no single node can take a decision in isolation. Even other participants have a role in decision-making regarding governance through the casting of votes. Related: What are governance tokens, and how do they work? Web3 transactions are practically irreversible and traceable, thus ruling out any possibility of someone making changes in the database post-transaction. This makes Web3 a potent tool against fraudulent behavior. Automation Smart contracts automate the system that can function without any human intervention. The code reflects the agreement between various stakeholders, executing transactions that cannot be reversed. Smart contracts substantially bring down operational costs, eliminate prejudice and make transactions more secure. Projects, however, have to be careful about vulnerabilities in smart contracts code that hackers can take advantage of to steal the booty. This can be overcome by getting the smart contract code thoroughly audited by a team having a proven track record in vulnerability assessments using a mix of manual and automated tooling. A Web3 example of accelerating automation is Zokyo, which specializes as an end-to-end security resource for blockchain-based projects. Creator economy Nonfungible tokens (NFTs), a component of the Web3 ecosystem, have added another dimension to the web economy. These tokens make each digital asset unique in some sense. Regardless of the number of times it is duplicated, there is some way to distinguish it. This feature is useful to safeguard these assets against online forgery and maintain exclusive rights of the owner over their assets. In Web3, NFTs could serve as metaverse assets, game assets, certifications and whatnot, opening up endless possibilities and empowering content creators to make money in an unprecedented manner. Earlier, when audiences consumed the content of a creator, the audience only had the emotional or intellectual benefit. Thanks to NFTs, creators were now able to turn their community members into investors and provide them with some tangible value out of the interaction. For instance, if someone has started a group on a decentralized social media site, the first 50 subscribers might be rewarded with redeemable NFTs if they spend a certain amount of time interacting there. Contrary to what many think, one doesn’t need to have the technical know-how to create an NFT-based economy. No code solutions such as NiftyKit are available for various development needs like building NFT smart contracts, revenue splits, embeddable SDKs (software development kits), token gating and more. Without any coding, one can begin building a creator economy.
Čítaj viac