Why a 2017 Linux bug is now a major concern for the crypto industry
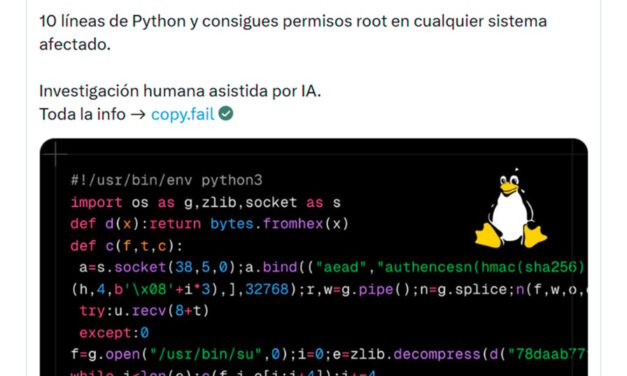
1. Copy Fail: The Linux vulnerability affecting crypto infrastructure securityA recently uncovered security flaw in Linux is drawing concern from cybersecurity specialists, government agencies and the cryptocurrency sector. Codenamed “Copy Fail,” the vulnerability affects many popular Linux distributions released since 2017.Under specific circumstances, the flaw could let attackers escalate privileges and gain full root control of affected machines. The Cybersecurity and Infrastructure Security Agency (CISA) has added the issue to its Known Exploited Vulnerabilities catalog, highlighting the serious threat it poses to organizations worldwide.For the crypto industry, the implications go well beyond a standard software bug. Linux powers much of the underlying infrastructure for exchanges, blockchain validators, custody solutions and node operations. As a result, an operating system-level vulnerability could create significant disruptions across large parts of the cryptocurrency ecosystem.2. What is “Copy Fail”?“Copy Fail” refers to a local privilege-escalation vulnerability in the Linux kernel, identified by security researchers at Xint.io and Theori.In simple terms, it allows an attacker who already has basic user-level access on a Linux system to elevate their permissions to full administrator or root control. The bug stems from a logical error in how the kernel handles certain memory operations within its cryptographic components. Specifically, a regular user can influence the page cache, the kernel’s temporary storage for frequently accessed file data, to gain higher privileges.What stands out about this vulnerability is how easy it is to exploit. A compact Python script, requiring minimal changes, can reliably trigger the issue across a wide range of Linux setups.According to researcher Miguel Angel Duran, it only requires roughly 10 lines of Python code to gain root access on affected machines.3. Why this vulnerability stands out as particularly riskyLinux security issues range from highly complex attacks that require chained exploits to simpler ones that need just the right conditions. “Copy Fail” has drawn significant attention because it requires relatively little effort after an initial foothold.Key factors contributing to the vulnerability include:It affects most mainstream Linux distributions.A working proof-of-concept exploit is publicly available.The issue has existed in kernels going back to 2017.This mix makes the vulnerability more concerning. Once exploit code circulates online, threat actors can quickly scan for and target unpatched systems.The fact that such a critical flaw stayed hidden for years underscores how even well-established open-source projects can contain subtle vulnerabilities in their foundational code.Did you know? The Bitcoin white paper was released in 2008, but Linux dates back to 1991. That means much of today’s crypto infrastructure is built on software foundations older than many blockchain developers themselves.4. How the “Copy Fail” exploit worksIt is important to first understand what full “root” control means on a Linux server. Root access is essentially the highest level of authority over the machine.With it, an attacker could:Add, update or delete any softwareView or steal confidential files and keysModify critical system settingsAccess stored wallets, private keys or authentication credentials if they are present on the affected systemTurn off firewalls, monitoring tools or other defensesThe exploit takes advantage of how the Linux kernel manages its page cache. The system uses a small, fast memory area to speed up file reading and writing. By abusing how the kernel handles cached file data, an attacker can trick the kernel into granting higher privileges than intended.Crucially, this is not a remote attack that can be launched from anywhere on the internet. The attacker first needs some form of access to the target machine. For instance, they could gain access through a compromised user account, a vulnerable web app or phishing. Once they have that initial foothold, the attacker can quickly escalate their permissions to full root control.5. Why this matters for the cryptocurrency industryLinux is widely used across cloud, server and blockchain node infrastructure, making it important to many crypto operations.Core parts of the crypto ecosystem run on it, including:Blockchain validators and full nodesMining farms and poolsCentralized and decentralized cryptocurrency exchangesCustodial services and hot/cold wallet infrastructureCloud-based trading and liquidity systemsBecause of this deep dependence, a kernel-level vulnerability like “Copy Fail” can create indirect but serious exposure across the crypto world. If attackers successfully exploit it on vulnerable servers, the possible consequences include:Stealing private keys or administrative credentialsCompromising validator nodes to disrupt operations or support broader network attacksDraining funds from hosted walletsCausing widespread downtime or launching ransomwareExposing user data stored on affected systemsWhile the vulnerability does not attack blockchain protocols directly, breaching the underlying servers that support them can still lead to major financial losses, reputational damage and operational disruption.Did you know? Major crypto exchanges rely on large-scale cloud, server and Kubernetes infrastructure to process trading activity, run blockchain nodes and support market-data operations around the clock. Coinbase, for example, has publicly described infrastructure tied to blockchain nodes, trading engines, staking nodes and Linux production environments. 6. Why initial access still poses a major threat in crypto environmentsSome users downplay this vulnerability because it requires a certain level of existing access to the target system. However, most real-world cyberattacks unfold in multiple phases rather than striking all at once.A typical attack sequence looks like this:Attackers first break in using phishing campaigns, leaked passwords or infected applications.They secure a basic foothold with ordinary user-level rights.They then use flaws like “Copy Fail” to quickly escalate to full administrator privileges.From there, they expand their reach across the network.This pattern is especially dangerous in the cryptocurrency space, where exchanges, node operators and development teams are prime targets for phishing and credential theft. What starts as a minor breach can quickly escalate into a full takeover when reliable privilege-escalation tools are available.7. Why security teams are particularly concernedCISA’s decision to include “Copy Fail” in its Known Exploited Vulnerabilities (KEV) catalog signals that the flaw is viewed as a high-priority risk.Red flags include the public release of working exploit code. As soon as proof-of-concept scripts become widely available, threat actors begin automated scans to look for unpatched systems to target.Many organizations, particularly in finance and crypto infrastructure, also tend to delay kernel updates. They prioritize system stability and avoid potential downtime or compatibility issues. However, this approach can leave systems exposed for longer during critical vulnerability windows, giving attackers more time to strike.Did you know? In simple terms, “root access” is like having the master key to an entire building. Once attackers gain it, they can potentially control nearly every process running on the system, change protected files and interfere with core security settings.8. The AI connection: Why this vulnerability could signal bigger challenges aheadCopy Fail was disclosed at a time when the cybersecurity world is increasingly focused on the role of artificial intelligence in vulnerability discovery.The timing coincides with the introduction of Project Glasswing, a collaborative effort backed by leading tech organizations such as Amazon Web Services, Anthropic, Google, Microsoft and the Linux Foundation. Participants in the project have highlighted how rapidly advancing AI tools are becoming better at identifying and weaponizing weaknesses in code.Anthropic has stressed that cutting-edge AI models are already outperforming many human experts when it comes to finding exploitable bugs in complex software. The company says these systems could greatly speed up both offensive and defensive cybersecurity work.For the cryptocurrency industry, this trend is particularly concerning. Crypto systems are high-value targets for hackers and are often built on layered open-source technologies, making them potentially more exposed as AI-driven attack methods evolve.9. What this means for everyday crypto usersFor most individual crypto holders, the direct risk from this specific Linux issue remains low. Everyday users are unlikely to be personally singled out.That said, indirect effects could still reach users through:Breaches or downtime at major exchangesCompromised custodial platforms holding user fundsAttacks on blockchain validators or node providersDisruptions to wallet services or trading infrastructureSelf-custody users should take note if they:Run their own Linux-based blockchain nodesOperate personal validators or staking setupsMaintain crypto-related tools or servers on LinuxUltimately, this situation highlights an important reality: Strong crypto security is not just about secure smart contracts or consensus mechanisms. It also depends heavily on keeping the underlying operating systems, servers and supporting infrastructure up to date and protected.10. How to stay protected“Copy Fail” is a reminder of how quickly underlying operational vulnerabilities can escalate into major security threats in the digital space. The positive side is that most of these risks are manageable. Organizations and users can significantly reduce their exposure by applying security updates promptly, enforcing stricter access controls and maintaining strong overall cybersecurity practices.For cryptocurrency organizations and infrastructure teamsCompanies running Linux-based systems should prioritize these steps:Deploy official security patches as soon as they become availableMinimize and strictly control local user accounts and permissionsRegularly audit cloud instances, virtual machines and physical serversSet up strong monitoring for unusual privilege-escalation attemptsStrengthen SSH access, key-based authentication and overall login securityFor everyday crypto usersIndividual holders can lower their exposure by:Keeping operating systems and software fully updatedAvoiding downloads from unverified sources or unofficial crypto toolsUsing hardware wallets for significant holdingsEnabling multi-factor authentication (MFA) wherever possibleIsolating high-value wallet activities from everyday computers and browsersFor node runners, validators and developersThose managing blockchain nodes or development environments should:Apply kernel and system updates without delayClosely follow Linux security bulletins and advisoriesReview container setups, orchestration tools and cloud permissionsLimit full administrator rights to the bare minimum
Čítaj viac